I’m impressed how some software Vendor have resisted to provide support for Red Hat Enterprise Linux 6 (RHEL6) and its derivates for their products. This week I ran into two examples:
WebOS Security
I had the pleasure of attending WebOS Developer Workshop in Mainz on Saturday Thgtwi (@thgtwi) did a great job with the organization. SuVuK(@SuVuK_open) did a nice report on the contents of the Workshop in his blog.
I took the opportunity talk about Security in the WebOS platform. I ran some tests based on WebOS 3.X, which is currently available for the HP TouchPad and is being opensourced as Open WebOS. Keep Reading →
Followup on mind control

Mae Geri. Source: http://www.foto-harz.de/details.php?image_id=968
This post was originally going to be dedicated to Karate, but I stumbled upon a reflective article: “Mind Control” by Pete Herzog and decided to try to build on top of it.
Pete, makes reference that given the speed of our sensors and our brain we basically live in the past: 80 ms in the past to be precise. So since we live in the past, our mind has been made up before we actually know or realize it; this enables us to perform complex tasks in “mental autodrive” or mental cruise control and how much energy is necessary to change mental patterns. Keep Reading →
Implementing effective controls: Venezuela to block stolen mobile phones
Even though a don’t agree with many of the decisions and laws created in Venezuela, I think this is great example of implementing a control for a big risk. Keep Reading →
Empathy and MSN
I’ve had some problems recently (the last couple of weeks) with Empathy on Ubuntu 10.04. All my MSN accounts just started giving my an “Authentication Failed”.
After checking with pidgin, which I use for other accounts, that my credentials were still working I found a post in the Ubuntu Forums that gave me a good solution:
$ sudo aptitude remove telepathy-butterfly
— Make sure you have telepathy-haze installed, if not
$ sudo aptitude install telepathy-haze
— Delete the accounts and recreate them with the new plugin
I’m not sure why this happened, but at least it’s working again.
Hope this helps someone else out there.
ooimpress and .pps files
I’ve been working with Ubuntu lately at the day job and the Open Office setup is different than on Fedora. One special case is the opening of .pps files, which per default go into “presentation mode” which I normally hate to see (it just takes to long to see what you really what to see in the presentation.
This is a workaround I found around in the Web:
Create ~/bin/ooimpress-edit or if you want to use it system wide /usr/local/bin/ooimpress-edit; and add the following code into it
#!/bin/bash
ooimpress -n “$*”
exit
Use it when ever you think you need it. I set it up as default behaviour in the browser.
Enjoy
Lucid Lynx and Constantine multiboot
As most of you know I’m a Fedora user, well started out some time ago as a Redhat user until they decided to have to spins: Redhat (stable for the enterprise) and Fedora (bleeding edge for the community). Back to the point, my main distro is Fedora but I like to give other distributions a spin to find the pros and cons.
I decided to install the new and shiny Ubuntu 10.04 “Lucid Lynx”, but there is no way I want to affect my main partitions!! Why should I this is Linux after all, it can boot from a secondary partition I can even put the bootloader at the beginning of the partition to make it totally independent!! Having done that already with Backtrack 4, Ubuntu 9.10 (karmic) and CentOS 5.x it should be as easy as 1 – 2 – 3 (Or simple as… got Jackson 5 ringing in my ear right now).
So the solution I had in mind was just to add a new partition with parted, install there and add the following lines to the /etc/grub.conf in my Fedora partition:
title Ubuntu 9.10 (Karmic)
rootnoverify (hd0,6)
chainloader +1
The problem is that Ubuntu 10.04 ships with grub-2 (technically speaking 1.98) and it just doesn’t work the same way. After a couple of re-installs and hours later I came out with this blog with a really detailed review of the distribution and with the solution I needed:
title Ubuntu 10.04 (Lucid Lynx)
root (hd0,4)
kernel /boot/grub/core.img
savedefault
boot
Just to make sure your a attacking the right error, this is was I was getting: Error 13 invalid or unsupported executable format
Enjoy
Ubuntu Firefox: This address is restricted
I got the weirdest of errors today trying to open a web page on port 6000: 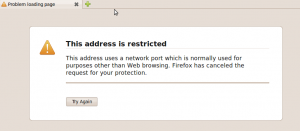
After reading for a while I found out that de Mozilla Foundation built in this protection for “Cross-Protocol” scripting attack with a form of Port Banning.
To overide this protection use one of the following steps:
- In the user’s profile directory the all.js, add the following line at the end of the file
user_pref("network.security.ports.banned.override", "1-65535"); - In the defaults/pref/ sub-directory of the installation directory (multi-user systems) add the following line at the end of the file
user_pref("network.security.ports.banned.override","1-65535"); - Open a new window, in the address type: about:config and add a new entry of the type string with this name network.security.ports.banned.override and value 1-65535.
If you want to set free only one port change the range for that port o list of ports.
US Access to SWIFT data
This is a topic that caught my eye a while ago and just found out it’s still an open issue.
According to their website:
SWIFT is the Society for Worldwide Interbank Financial Telecommunication, a member-owned cooperative through which the financial world conducts its business operations with speed, certainty and confidence. Over 8,300 banking organisations, securities institutions and corporate customers in more than 208 countries trust us every day to exchange millions of standardised financial messages.
So basically it’s the organization that manages the API’s and systems that make international banking work smoothly.
This Belgium based organization had it’s major databases in the US until an article in the NY Times aired that the CIA under the Bush administration had been data mining the database to find links to terrorism, after Europe protested the database was move to Holland. So the issue now is that the US intelligence agencies want to keep having unlimited access to spy on EU Citizens using the usual terrorism joker card.
I think this is a big issue and should be handled a such. There are some open questions I have to this deal:
What does a US or in fact any intelligence agency have to do with our financial records without a warrant?
Is every person in the world considered a potential terrorist?
Were are rights, are privacy?
While we’re at it: How long is this data retained? How is it guarded? Who makes sure it’s correctly discarded?
Benjamin Franklin summed this up better than I can ever try to:
They that can give up essential liberty to obtain a little temporary safety deserve neither liberty nor safety