I like attending conferences, they provide a front row seat to the lastest research and other people in your area are doing and thinking. For me they are inspiring. They also provide a great space for networking and getting to know great people, especially in our security community.
Around the conference, there is normally a lot going on, and I normally miss out on most of it because I’m focused on the talks. So this time, I decided to skip the conference all together and just visit the Haxpo (or the program around the main conference)
Hack in the Box (Amsterdam) is a great event, I’ve attended a couple of times: trainings and talks. They also organize a great Expo, it runs parallel to the conference and always has a lot to offer. This piece covers my day at the Haxpo.
After a quick recognition round, I decided to split my time in the different challenges, and there were many: chip-off, capture the signal, IoT, car hacking, building automation, and medical.
First off, I went to the Chip-off challenge. These guys brought a box full of broken USB sticks and three stations fully equipped with all the tools necessary to remove flash chips from the sticks and place them in special readers and extract the data.
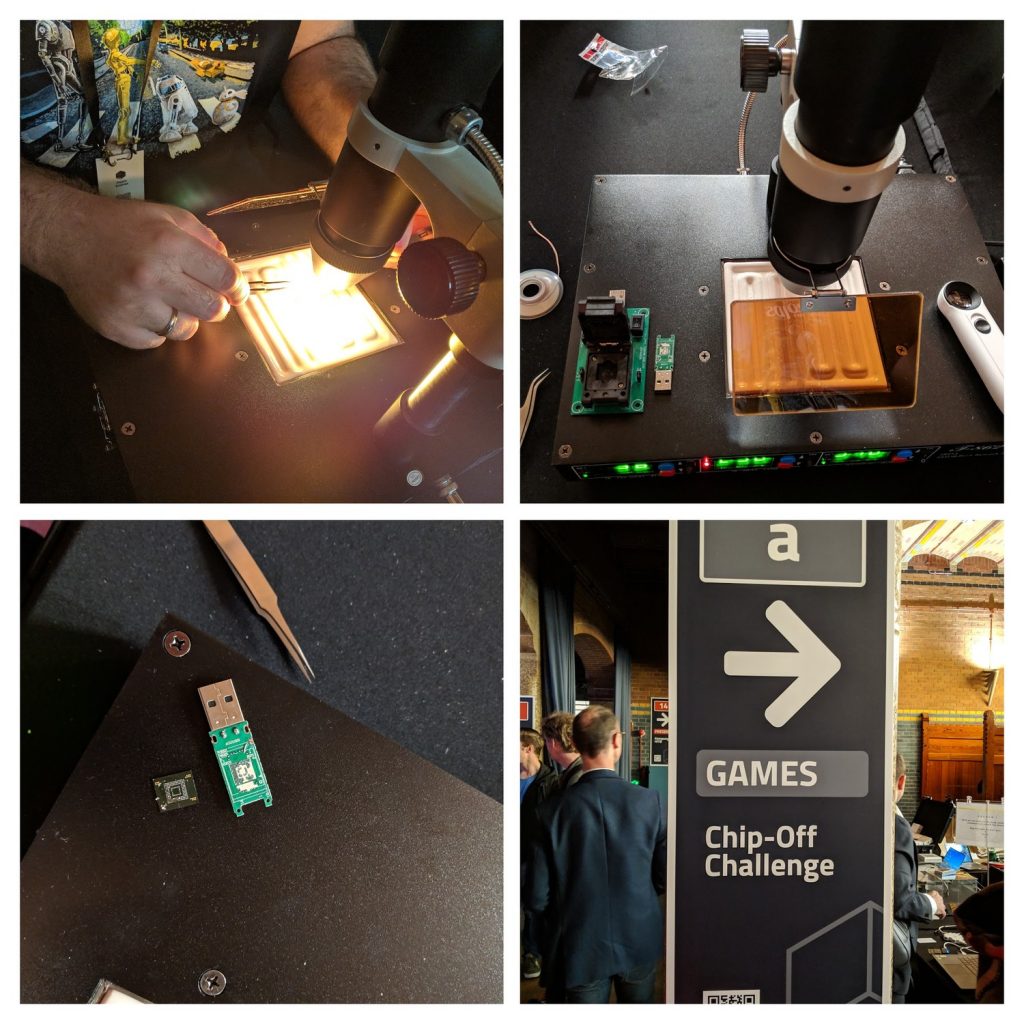
The process is simple: heat the PCB and chip from all sides until the chip just comes off using the tweezers. Then proceed to remove any excess of solder. Once the chip is clean, it can be placed in the reader making sure that the you place it with the notch in the right corner
I got lucky and my flash chip was working. I took a quick look at the data, but decided not to take it, who knows what it actually was and contained.
Next stop was the car hacking village. They had two big boxes that contained all the relevant parts to hack. head unit, entertainment center, ECUs, and even the blinker lever… I received a very short intro into the challenge, the tool and how this all worked. The learning curve is pretty steep, but after a while I was hacking away: I managed to make the fuel tank indicator point to empty!

There were two types of challenges. Changing the values on indicators and making lamps turn on and off, like the check engine lamp. The first ones were easy, because a sensor is constantly sending a value to the head unit, so it is a mater of seeing the traffic in the CAN bus, and injecting messages faster than the sensor. The lamps where harder, because you had to look up the standard and hope that that make and model followed it.
My next stop was the IoT hacking village. It was maned by they guys from NullCon. There were multiple challenges which included hacking device with known vulnerabilities, like smart bulbs and a BLE lock, and there very own Diva board. This board allows one to perform some hardware hacking using different serial protocols and interfaces, like UART, JTAG, SPI and I2C.
After lunch, I moved on to the medical device village. Different devices where here to be played with, from a heart monitoring station to an eco-machine. It was interesting to be able to play with them, somehow it is frowned upon in hospitals ?
I met up with Slawomir Jasek at the RFID village. There I learned how to use his app to clone RFID cards and could also use the Mark IV, to clone different kinds of cards using the card readers installed on some mini doors.

I visited the stand of the guys from Applied Risk. They built up some really cool setups to hack: an industrial process using real PLCs and a doll house using: a building management system, RFID reader for access control, video camera surveillance and a video conference system.
Someone from their team was presenting vulnerabilities on the building management system, so the focus was there. I found the vulnerable pages on the web GUI, but since the default password didn’t work, I could not find the right parameters for the injection. The camera and conference room did fall easily.
My last stop was the Capture the Signal. This was an entire capture the flag setup based on RF or wireless hacking. The first signal was being transmitted live and you could work your way through all the challenges. Some of the signals were being transmitted via URSP and actually being captured live somewhere else.
After a long day, I stepped outside to get something to eat and sit in the nice Amsterdam sun. Later on I joined the TCP/IP networking party and even managed to have a short chat with Dhillon Kannabhiran.
I had a blast! I knew that there was lots to do, but I never thought that I would be so busy, would have so much fun and would meet that many interesting people. I will definitely be back next year, hopefully as a trainer.
This post was originally posted at LinkedIn Pulse, here.

Recent comments